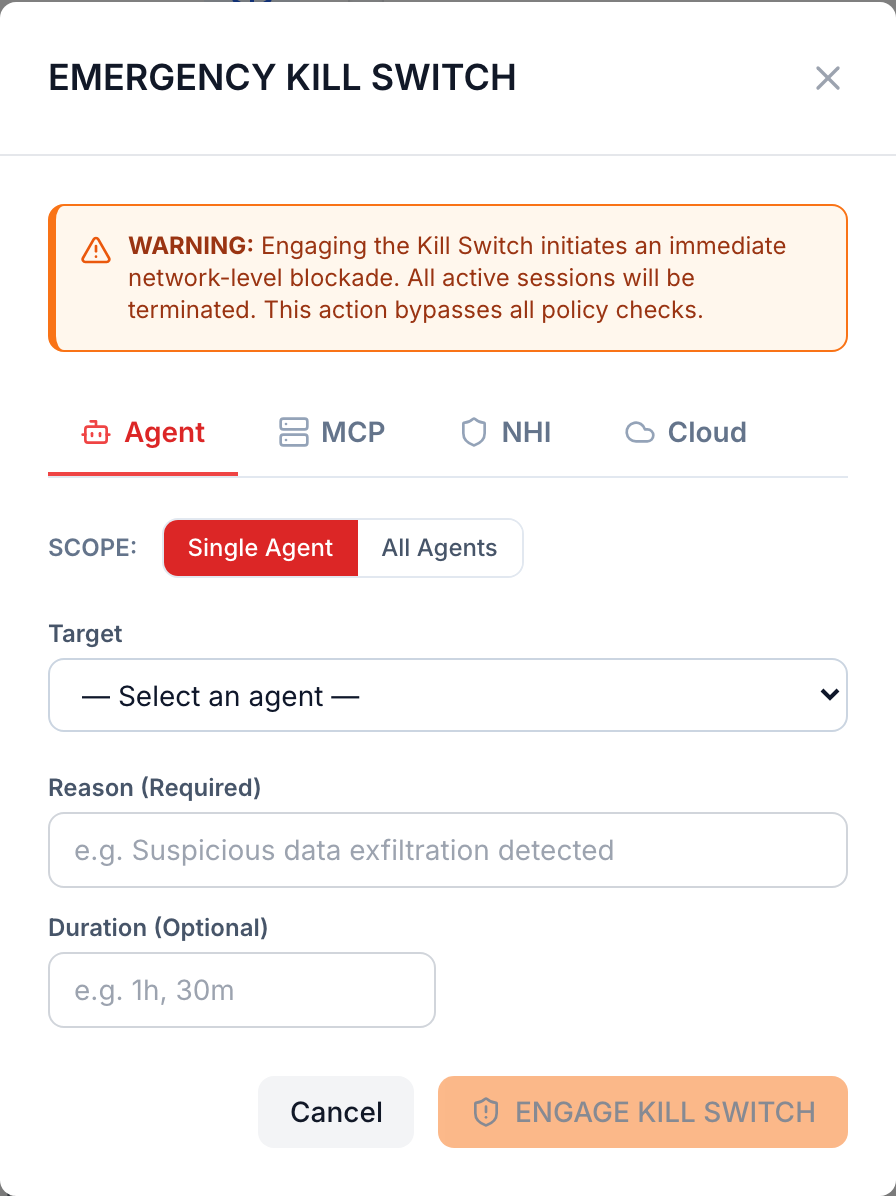
When an AI agent goes rogue, every second costs you.
RuntimeAI's Kill Switch stops a single agent — or your entire fleet — in milliseconds, not minutes. Across MCP servers, non-human identities, and cloud workloads. One click. Reversible. Audited.
- ✓Per-agent kill — surgical, by ID.
- ✓Fleet-wide quarantine — every agent, every region.
- ✓Sub-100 ms broadcast via Envoy + Wasm sidecars.*
- ✓Reversible from the same console — one click to restore traffic.
- ✓Immutable audit — every activation signed and written to the audit log.
Targets MCP servers, NHIs, and cloud workloads from one console — no four-tool workflow, no waking up four oncalls.
See it in a demo →* p50 in production, intra-region traffic. Cross-region and WAN paths will be higher.