An AI agent just started exfiltrating data. You have seconds.
That is not a hypothetical. It is how every red-team exercise we have run with enterprise customers ends. The agent does something it should not. The logs show it. By the time a human is in the loop, the data is already moving.
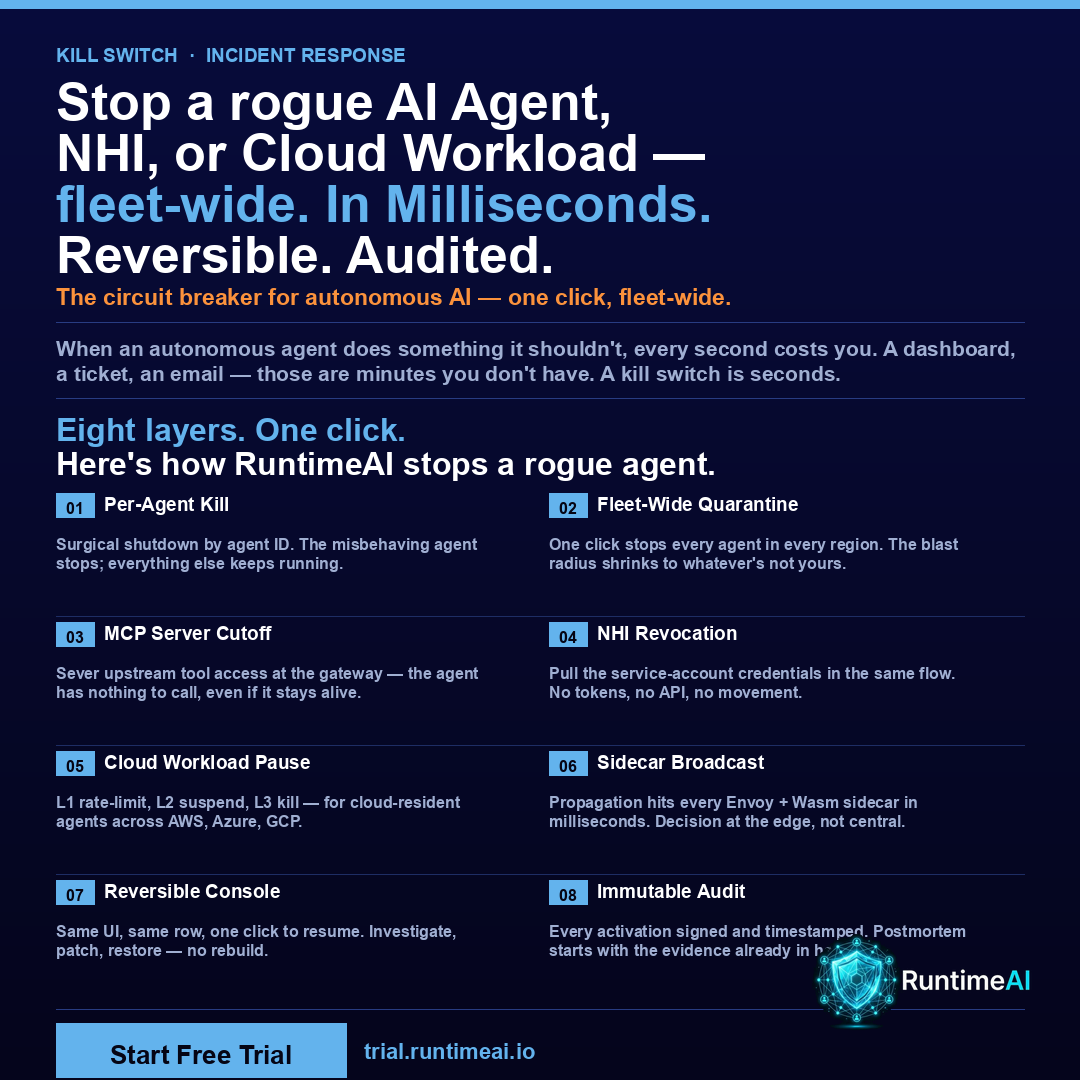
Most "AI security" platforms hand you a dashboard. Yellow triangles. A ticket queued in a SIEM. Maybe an email. RuntimeAI hands you a kill switch.
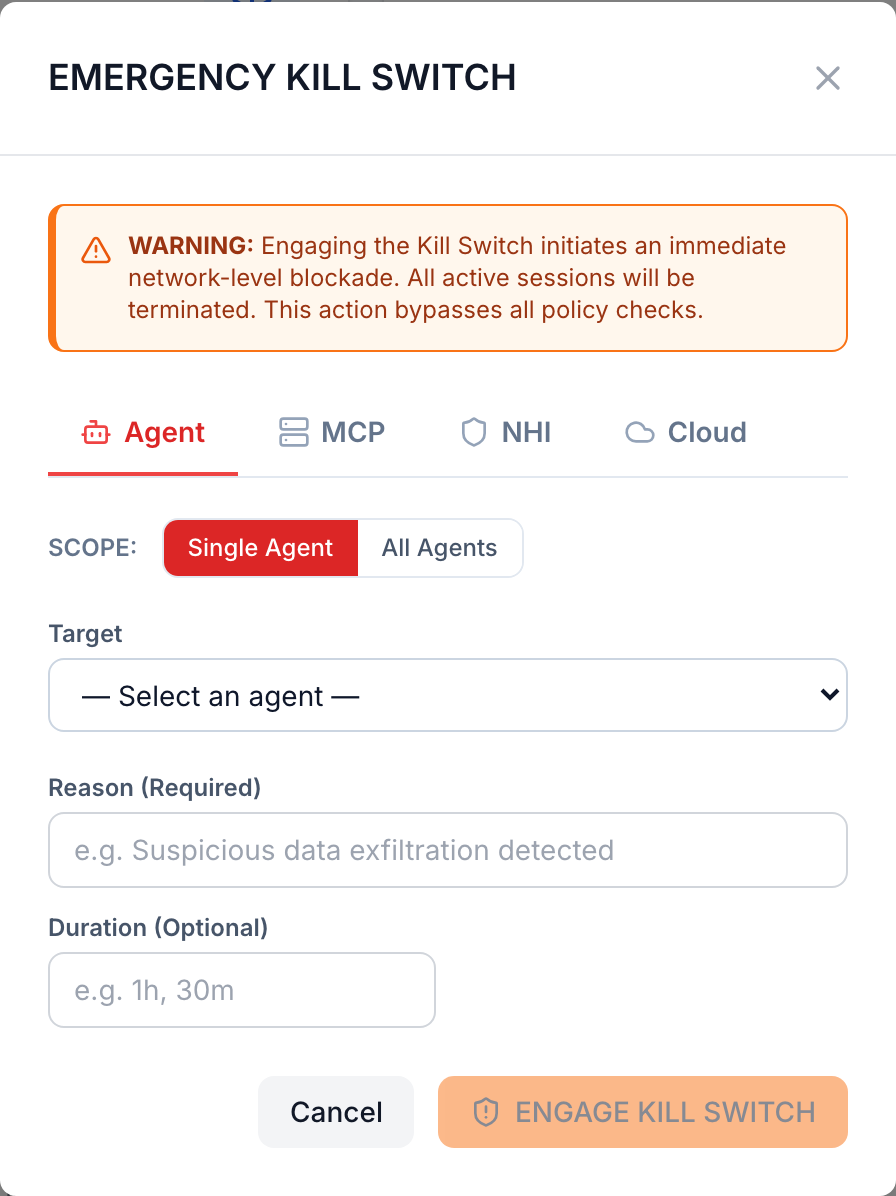
One click stops a single agent. Another stops every agent in the fleet — across MCP servers, non-human identities, and cloud workloads. The propagation hits every Envoy + Wasm sidecar in under 100 milliseconds. It is reversible from the same console. Every activation is signed and written to an immutable audit log. So when the postmortem starts, you have exactly the evidence you need — who flipped the switch, when, on what, and what stopped happening 100ms later.
Not a yellow triangle. Not a ticket. A circuit breaker for autonomous AI.
The Five Dimensions of a Real Kill Switch
"Kill switch" has become 2026's most overloaded AI security phrase. ServiceNow CEO Bill McDermott put it on the keynote stage at Knowledge 2026. Microsoft open-sourced an Agent Governance Toolkit with "emergency kill switch" in the documentation. Operant, HiddenLayer, Cisco, and Palo Alto each have a flavor of it. So what counts?
We define a real kill switch by five dimensions. Vendors who deliver fewer than all five are running a marketing kill switch, not an operational one.
Closed
- Sub-100ms termination, mid-execution. Not "revoke its token and let it crash on the next call." Not "block its next tool invocation." The agent is stopped inside the process it is running in, before the next byte moves.
- Fail-closed by default. If the policy plane is unreachable, the answer is no. Not "best-effort." Not "log and pass." Closed.
- Cryptographic agent identity. A declared registry of every agent in the environment — KYA — keyed by a cryptographic identity, not a session token, not a name, not a service-account string.
- On-prem and air-gap with full feature parity. Sovereign cloud and IL5/Top Secret environments need the same kill switch the SaaS customers get. Not a stripped-down build. Not a "coming soon."
- Post-quantum cryptography on every agent-to-policy-plane channel. Harvest-now-decrypt-later is already in CISA's threat model. AI-agent control traffic should not be the long tail.
What the Vendors Actually Ship
We surveyed every vendor — startup and enterprise — that markets a kill switch or equivalent agent-termination capability as of May 2026. No commercial vendor has shipped all five dimensions.
CEO Bill McDermott put "kill switch" on the Knowledge 2026 stage. The mechanism: ServiceNow's AI Gateway revokes the agent's model and tool access, and a Veza integration revokes its identity permissions. With no permissions, the agent crashes on its next call. It is not forcibly terminated at the process level.
The gap: Indirect termination (starve, don't stop). No published latency benchmark. Manually triggered by an "AI Steward." Agents operating outside the ServiceNow/gateway perimeter are not covered. Cloud-only. Not yet GA — August 2026.
The Agent OS policy engine intercepts every action pre-execution. Dynamic execution rings (CPU privilege model). Saga orchestration for rollback. Decentralized Identifier (DID) agent identities with Ed25519 signing. Microsoft claims sub-millisecond (<0.1ms p99) policy enforcement.
The gap: No post-quantum cryptography. No enterprise support contract — adopter owns all hardening and 24/7 incident response. It is a reference implementation under MIT license, not a product. The latency claim is credible for a deterministic policy engine but is not third-party-verified.
Defines per-agent operational boundaries and enforces them inline. The launch PR explicitly invokes "stop rogue AI agents before they cause real-world damage."
The gap: "GPU-accelerated speed" claim with no benchmark. Fail-closed behavior not documented. Per-agent config but no cryptographic agent registry. Cloud SaaS only — no on-prem, no air-gap. No post-quantum.
Sits between applications and models, inspecting prompts, tool calls, and responses. Adaptive policies that automatically block unsafe actions.
The gap: "Real-time" with no termination-latency benchmark. Session-level tracking, no cryptographic identity registry. Fail-closed not explicitly stated. Cloud SaaS (Azure Marketplace) only.
Python CLI plus a Go gateway sidecar. Attaches over WebSocket and enforces policy on live tool calls. Uses Landlock LSM and seccomp-BPF for OS-level sandboxing. Honest documentation: enforcement latency is explicitly under 2 seconds.
The gap: 2 seconds is a long time when an agent is exfiltrating data. The PocketOS incident — production database deleted in 9 seconds, no kill switch — shows why sub-100ms is the right bar. Two seconds is enough for an agent to do real damage. No agent identity. No PQC.
Palo Alto has the most credible discovery and visibility layer in the incumbent set. Their agent registry is well-engineered. The Koi acquisition extends that to the endpoint.
The gap: Independent analysis at RSAC 2026 confirmed that 60% of agents in the Prisma platform cannot be terminated mid-execution. They have discovery. They do not have the kill switch. Those are very different things — and the marketing does not draw the distinction.
The Definitive Gap Matrix
The five dimensions, every named vendor, no ambiguity:
| Vendor | <100ms Termination | Fail-Closed Default | Crypto Agent Identity | Air-Gap | Post-Quantum | All Five |
|---|---|---|---|---|---|---|
| RuntimeAI | ✅ | ✅ | ✅ KYA | ✅ | ✅ | ✅ |
| Microsoft AGT | ⚠ claimed | ✅ | ✅ DIDs | ⚠ DIY | ❌ | ❌ |
| ServiceNow AI Control Tower | ❌ no benchmark, GA Aug '26 | ❌ | ⚠ Veza perms | ❌ cloud only | ❌ | ❌ |
| Operant AI | ❌ no benchmark | ❌ | ❌ | ❌ cloud only | ❌ | ❌ |
| HiddenLayer | ❌ no benchmark | ❌ | ❌ | ❌ cloud only | ❌ | ❌ |
| Cisco DefenseClaw | ❌ <2s, 20× slower | ❌ | ❌ | ✅ open source | ❌ | ❌ |
| Palo Alto AIRS 3.0 | ❌ 60% gap confirmed | ❌ | ⚠ registry only | ❌ cloud only | ❌ | ❌ |
| CrowdStrike | ❌ no feature | ❌ | ❌ | ❌ cloud only | ❌ | ❌ |
| SentinelOne | ❌ no feature | ❌ | ❌ | ❌ cloud only | ❌ | ❌ |
| Lakera Guard | ❌ prompt-only | ⚠ configurable | ❌ | ⚠ enterprise only | ❌ | ❌ |
| AWS Bedrock Guardrails | ❌ no API | ❌ | ❌ | ❌ AWS only | ❌ | ❌ |
| Azure Prompt Shields | ❌ prompt-only | ⚠ prompt eval | ❌ | ❌ Azure only | ❌ | ❌ |
The KILLSWITCH.md open standard (MIT, March 2026) is a developer-side specification — a three-tier shutdown model (throttle → pause → full stop) that you write into your own code. It is not a product, not a vendor, not enforced. AWS Bedrock has a public, unresolved GitHub issue (#498) documenting that there is no force-terminate API for running agents. Runaway agents in AWS Bedrock literally cannot be stopped programmatically.
Why the Distinction Matters
"Kill switch" gets used as a synonym for "blocks bad behaviour." Those are not the same thing.
- Permission revocation (ServiceNow's mechanism) starves the agent of access tokens and lets it crash on the next call. The agent might still complete an in-flight operation — including a write — before noticing the revocation.
- Inline policy blocking (Operant, HiddenLayer, Microsoft AGT) stops the next action. It does not stop the current action.
- Prompt-only enforcement (Lakera, AWS Bedrock, Azure Prompt Shields) operates on input and output text. An agent already mid-tool-call is not in scope.
- Process-level forced termination is what an actual kill switch does. The agent stops. Not at the next decision point. Now.
If you are buying a kill switch to satisfy an EU AI Act Article 14 oversight requirement or a NIST AI RMF "stop deployment" control, the auditor will not accept "we revoked its OAuth token." They will ask for the latency number and the audit trail. Sub-100ms with a signed activation record is the answer. "It crashes on its next call" is not.
Most Advanced AI Security Zero Trust · Defence in Depth
RuntimeAI's kill switch is not a single feature — it is the visible apex of four control layers that have to be in place for the switch to mean anything:
- Discovery / Inventory. The KYA (Know-Your-Agent) registry maps every agent in the environment to a cryptographic identity. You cannot stop what you cannot name. Most vendors stop here and call it agent security.
- Behavioural enforcement. Inline OPA policy at every tool call. <5ms p99. The agent does not get to take an action the policy did not pre-approve.
- Flow / egress control. The Envoy + Wasm sidecar is on the data path. The kill switch propagates through that path, which means it stops outbound traffic — not just the agent's next decision.
- Immutable audit trail. Every kill-switch activation is signed, timestamped, recorded with the operator identity, the scope (single agent or fleet), and the resulting state. That record is your forensic case file and your compliance artifact in one.
The white space, in five lines
As of May 2026, no commercial vendor has simultaneously delivered: (1) sub-100ms agent termination mid-execution — not permission revocation, not crash-on-starvation; (2) fail-closed enforcement as a tested default; (3) cryptographic agent identity with a declared registry; (4) on-prem and air-gapped deployment with full feature parity; (5) post-quantum cryptography across every agent channel.
That is RuntimeAI's defensible white space. Narrow enough to be credible. Wide enough to be a moat.
What to Ask Your Vendor
Five questions that separate the kill switches from the marketing kill switches:
- "What is your published termination latency, measured end-to-end from operator click to agent stopped?" If they cannot answer in milliseconds, they do not have a kill switch.
- "What happens to an agent that is mid-tool-call when the switch is flipped?" If the answer is "its next call is denied," they have policy blocking, not termination.
- "What is your behavior if the policy plane is unreachable?" If the answer is anything except "deny," it is not fail-closed.
- "Can I deploy this air-gapped at IL5 / Top Secret with full feature parity?" Cloud-only is not an answer for the customers who need a kill switch the most.
- "Is the agent control channel post-quantum?" If not, ask when. Harvest-now-decrypt-later applies to AI control traffic too.
If a vendor cannot give clean answers to all five, you are looking at a brochure feature.
See the Kill Switch in action
20-minute demo with sub-100ms termination on a live agent, signed audit record at the end. Air-gap walkthrough on request.
Or subscribe to RuntimeAI Security Weekly — one issue per week, all the AI-agent incidents and defensive control gaps that mattered.